Software patches are a foundational element of effective cybersecurity, delivering targeted fixes that close vulnerabilities and reduce exposure. A well-implemented patch management program coordinates discovery, testing, deployment, and verification to minimize downtime and reinforce software patching practices. When organizations pursue proactive patching and vulnerability remediation, they shrink the attack window and strengthen system hardening. Security updates are most effective when patch management ensures timely application across endpoints, servers, and applications. This approach supports resilience, reduces disruption, and underpins ongoing business continuity.
From a practical perspective, organizations rely on timely updates and security fixes to close weaknesses before threats exploit them. This LSI-driven framing embraces patching, remediation, and vulnerability management as interconnected activities that collectively reduce risk. Vendor advisories, testing in safe environments, and controlled deployment across endpoints form a coordinated effort to maintain continuity. A mature program also emphasizes visibility into assets, dependency care, and continuous hardening to sustain resilient operations.
The Strategic Importance of Patch Management in Cybersecurity
Patch management is the backbone of an effective cybersecurity posture. By coordinating the timely identification, testing, and deployment of patches across endpoints, servers, and applications, organizations reduce the attack surface that adversaries can exploit. A mature patching program supports vulnerability remediation by closing known weaknesses before attackers can exploit them and reinforces system hardening through consistent application of fixes and configuration improvements.
Beyond technical fixes, patch management aligns with governance, risk management, and uptime goals. It lowers the risk of ransomware and data loss by minimizing exposure, reduces downtime from exploit-related incidents, and enables continuous improvement through regular reporting, audits, and metrics that inform leadership decisions.
Understanding Software Patches: What They Do and Why They Matter
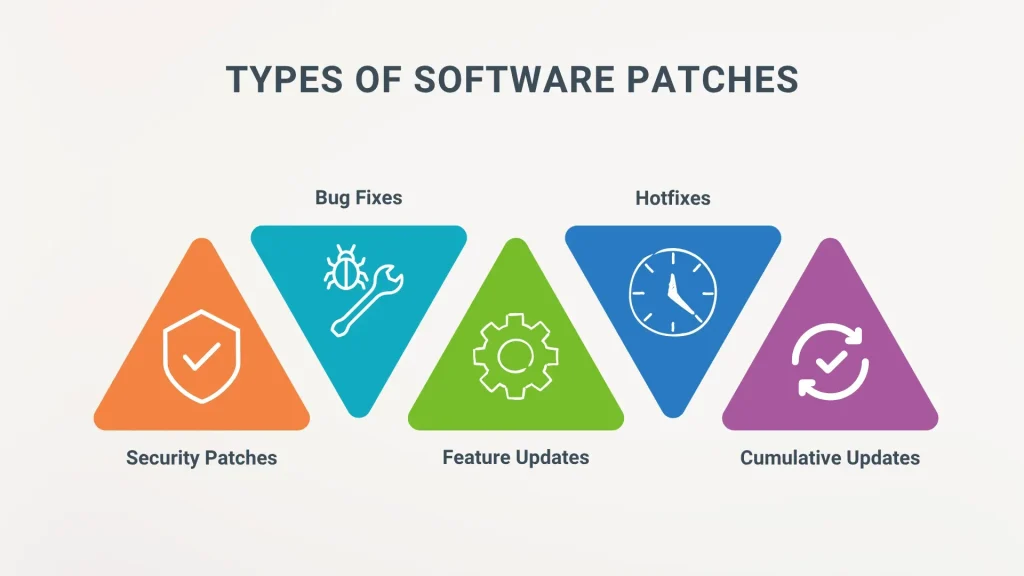
Software patches are changes released by vendors to fix bugs, close security vulnerabilities, and improve performance. They come in many forms—security patches, feature updates, and firmware patches—and when applied promptly they shrink the window of opportunity for attackers.
Timely execution of patches is a core part of vulnerability remediation, turning discovered weaknesses into mitigated risk. Security updates are a subset of patches specifically crafted to address threats in the wild, and a disciplined patching approach ensures these updates are deployed consistently across the environment as part of ongoing patch management.
The Patch Management Lifecycle: From Discovery to Verification
Patch management lifecycle begins with asset discovery and inventory, enabling you to know what needs patching and where to apply fixes. Then vulnerability identification and risk scoring determine which patches matter most, guiding testing and deployment planning within the patch management framework.
Testing patches in a controlled environment helps catch compatibility issues and avoid downtime in production. Verification and validation complete the loop by confirming successful patch installation, rescan for remnants, and maintaining governance through reporting to stakeholders.
Prioritizing Patches by Risk: A Risk-Driven Approach
Prioritizing patches by risk, not just severity, helps you allocate resources to critical vulnerabilities that expose sensitive data or critical services. Use CVSS, asset criticality, exposure, and exploit likelihood to rank patches within the patch management workflow and align with vulnerability remediation priorities.
Practical prioritization also considers business context, service levels, and user impact. This risk-driven approach reduces unnecessary testing time and accelerates remediation for high-risk systems, balancing patch management workloads with ongoing security objectives.
Automating Patch Deployment While Maintaining Governance
Automation accelerates software patching, patch deployment, inventory, testing, and reporting, but governance must stay strict. Patch management platforms, configuration management tools, and vulnerability management platforms form a layered approach that scales across operating systems and applications while maintaining control.
Pair automation with change management, rollback plans, and phased rollouts to minimize disruption. This ensures security updates are applied securely and consistently without compromising availability, contributing to system hardening and resilience.
Measuring Success and Driving Continuous Improvement in Patch Programs
Measuring patch program success requires metrics such as mean time to patch (MTTP), deployment rate, failure rate, and vulnerability remediation coverage. Dashboards and regular reviews keep leadership informed and drive continuous improvement in patch management performance.
Looking ahead, smarter patching leverages AI for threat-informed prioritization, image-based patching for cloud-native environments, and SBOM-based governance for supply chain security. These trends support stronger system hardening, faster vulnerability remediation, and more reliable security updates across complex IT landscapes.
Frequently Asked Questions
What are software patches and why do they matter for patch management?
Software patches are fixes released by vendors to address security flaws, improve reliability, or add features. When applied promptly, patches reduce the attack surface and strengthen defenses, making patch management essential for risk reduction. They also support system hardening by closing gaps across endpoints, servers, and applications.
How do security updates relate to software patches and vulnerability remediation?
Security updates are a subset of patches focused on protecting systems from threats, while vulnerability remediation is the broader effort to identify and fix weaknesses. In practice, patches are the action in the remediation loop: identify risk, apply a patch, verify the fix, and monitor for new threats. This continuous cycle keeps the organization resilient against evolving risks.
What is the patch management lifecycle from discovery to verification?
The patch management lifecycle includes: asset discovery and inventory; vulnerability identification and risk scoring; patch identification and testing; deployment planning and change management; execution and deployment; verification and validation; and reporting and governance. Each step ensures patches are applied effectively with minimal disruption and informed decision-making.
How can I build a reliable patch management program to minimize downtime when applying software patches?
Start with a clear patch policy and an accurate asset inventory. Prioritize patches by risk, test in a representative environment, and automate deployment where possible with strong governance and rollback plans. Plan downtime carefully, integrate patching with vulnerability management, and monitor results to support ongoing system hardening.
What are common patch management challenges and how can you overcome them?
Common challenges include downtime and user impact, compatibility issues, patch fatigue, shadow IT, and vendor delays. Mitigate these by scheduling patches during off-peak hours, using rollback mechanisms, maintaining comprehensive test suites, enforcing endpoint protection, automating where feasible, and coordinating with vendors and application owners.
What metrics indicate success for patch management and how do you drive continuous improvement in vulnerability remediation and system hardening?
Key metrics include mean time to patch (MTTP), patch deployment rate, patch failure rate and time to remediation, and policy compliance. Regular dashboards tied to vulnerability remediation progress and system hardening outcomes help leadership assess risk reduction and guide ongoing improvement.
| Aspect | Key Points | Notes / Examples |
|---|---|---|
| What are software patches and why they matter |
|
Zero-day exposure windows are closed when patches are applied promptly; mispatching can leave systems vulnerable. |
| Relationship between patches, security updates, and vulnerability remediation |
|
Continuous cycle sustains a robust security posture beyond ad-hoc fixes. |
| The patch management lifecycle (from discovery to verification) |
|
A mature pipeline reduces risk and downtime while improving auditability. |
| Practical steps to build a reliable patching program |
|
Clear policy plus disciplined execution reduces risk and ensures resilience. |
| Common challenges and how to overcome them |
|
Proactive planning mitigates disruption and accelerates remediation. |
| Patch management in practice: examples and best practices |
|
Automation enables scalable, repeatable patching across environments. |
| Automation, tooling, and the role of security teams |
|
Security teams coordinate between tools and stakeholders to maintain control. |
| Measuring success and driving continuous improvement |
|
Dashboards drive leadership buy-in and continuous improvement. |
| Future trends: smarter patching and proactive resilience |
|
Patches evolve as part of a broader strategy for resilient systems. |
Summary
Conclusion: Software patches are a critical line of defense in modern cybersecurity. A well-designed patch management program aligns people, processes, and technology to identify risks, test fixes, deploy updates, and verify outcomes. By prioritizing patches based on risk, automating where appropriate, and integrating patching with vulnerability management and system hardening efforts, organizations can reduce exposure, minimize downtime, and strengthen overall security posture. The journey from reactive patching to proactive security hygiene starts with a clear policy, accurate asset visibility, robust testing, and disciplined execution—so that software patches reliably protect rather than hinder business operations.